The FCC Ruling and the Rise of Open, Controllable WiFi Infrastructure
WiFi infrastructure is no longer just about connectivity — it is about control.
For years, decisions around WiFi deployments were driven by familiar factors:
performance, cost, and vendor relationships. Operators selected hardware, deployed
vendor-provided software stacks, and relied on proprietary management systems to
run their networks.
That model is now being challenged.
As WiFi becomes a critical layer of digital infrastructure — powering homes,
enterprises, campuses, and public networks — the stakes have changed. The
question is no longer:
“Which device should we deploy?”
It is now:
“Who controls the network stack?”
Recent regulatory developments, particularly the FCC’s actions around network
equipment, have accelerated this shift. But the implications go far beyond
compliance or hardware sourcing.
They point toward a fundamental transformation in how WiFi infrastructure is built,
operated, and controlled.
The Changing Landscape of WiFi Infrastructure
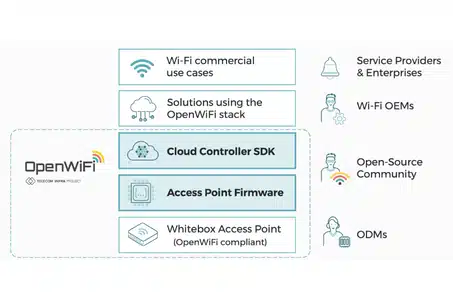
Traditionally, WiFi deployments have relied on tightly integrated systems:
- Closed firmware running on devices
- Proprietary cloud or controller platforms
- Limited visibility into internal behavior
This model offered simplicity, but it came with trade-offs:
- Vendor lock-in
- Limited flexibility
- Restricted innovation
For years, these trade-offs were acceptable because networks were viewed primarily
as operational tools.
That assumption no longer holds.
As WiFi infrastructure becomes critical to business operations, public services, and
national systems, the risks associated with opaque, vendor-controlled environments
are becoming harder to justify.
Operators today face several challenges:
- Security risks
Limited visibility into firmware and control planes makes it difficult to detect
vulnerabilities or verify behavior
- Supply chain dependency
Hardware sourcing is increasingly influenced by geopolitical and regulatory
factors
- Lack of control
Critical network decisions are dictated by vendor platforms rather than
operator needs
- Slower innovation
Customization and integration are constrained by proprietary ecosystems
In this context, relying on closed systems is no longer just a technical compromise — it becomes a strategic limitation.